Why Should My Business Use Penetration Testing?

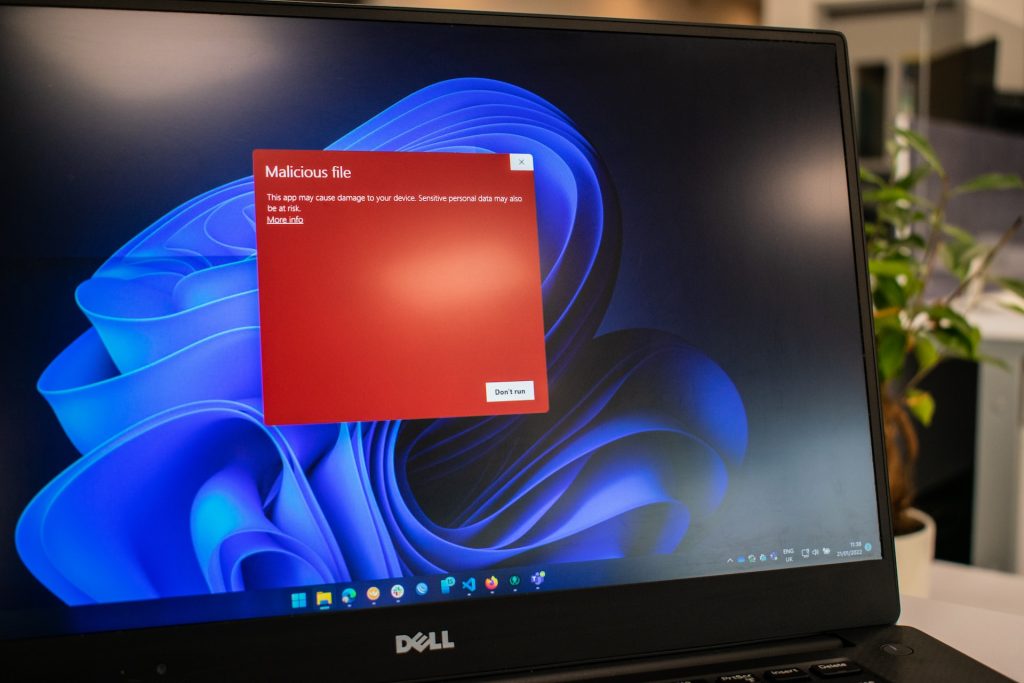
Businesses of all sizes face a variety of security threats that can compromise their sensitive data and cripple their operations. To ensure protection against cyberattacks, organisations must adopt proactive measures. One such measure is penetration testing, a vital component of a comprehensive security strategy.
Why should my business use penetration testing?
In an era where cyberattacks are rampant, it’s crucial to take pre-emptive action to identify vulnerabilities in your systems before malicious actors exploit them. Penetration testing, also known as ethical hacking, allows you to simulate real-world attack scenarios and uncover weaknesses that could be leveraged by cybercriminals. By proactively identifying and patching vulnerabilities, you can prevent costly breaches and protect your valuable business assets.
Benefits of Penetration Testing
Comprehensive Security Assessment
An effective penetration test provides a thorough evaluation of your organisation’s security posture. It goes beyond basic vulnerability scanning and examines the resilience of your network, applications and infrastructure. By emulating the techniques used by real attackers, penetration testing uncovers hidden weaknesses that may otherwise go unnoticed.
Early Detection of Vulnerabilities
Identifying vulnerabilities at an early stage is crucial to mitigating potential risks. Penetration testing allows you to detect weaknesses in your systems before they can be exploited. This enables you to address vulnerabilities promptly, reducing the window of opportunity for attackers and minimising potential damage.
Protection of Customer Data
Businesses have a responsibility to protect the personal information entrusted to them and the large amounts of data they hold. A single data breach can lead to severe reputational damage and legal repercussions. Penetration testing assists in identifying vulnerabilities that could expose sensitive customer data, allowing you to then implement the necessary safeguards and ensure compliance with data protection regulations.

Proactive Approach to Security
Taking a proactive stance towards security is important in the ever-evolving threat landscape. Penetration testing allows you to stay one step ahead of potential attackers. By regularly conducting tests and addressing vulnerabilities, you demonstrate a commitment to strong security practices, giving your customers, partners and stakeholders confidence in your business.
Validation of Security Controls
Implementing security controls and measures is not enough if they are not effectively tested and validated. Penetration testing provides an opportunity to assess the effectiveness of your security controls and determine their vulnerability to various cyber threats. This allows you to fine-tune your defences and ensure they are capable of withstanding real-world threats.
Cost Savings in the Long Run
While investing in penetration testing may seem like an added expense, it is a wise investment that can save your business substantial costs in the long run. By proactively addressing vulnerabilities, you mitigate the risk of data breaches, system downtime, legal fines and loss of customer trust. The cost of remediation and recovery from a breach far outweighs the expenses that come with conducting regular penetration tests.
These days where cyber threats are constantly in the news, businesses must take proactive measures to safeguard their data, systems and reputation. Penetration testing offers a powerful solution to identify vulnerabilities before they can be exploited by malicious actors. By conducting regular penetration tests, businesses can enhance their security framework, protect sensitive customer data and demonstrate a commitment to robust security practices.
Investing in penetration testing is an investment in the long-term success and resilience of your business. It allows you to stay one step ahead of potential attackers, detect vulnerabilities early and save costs associated with data breaches and recovery efforts. So, why should your business use penetration testing? The answer is simple: to fortify your defences, protect your valuable assets and ensure the trust and confidence of your customers.
FAQs about Penetration Testing
- What is penetration testing?
Penetration testing is a proactive security assessment technique that simulates real-world attacks on a company’s network, systems or applications. It aims to identify vulnerabilities and weaknesses that could be exploited by malicious actors.
- How often should penetration testing be conducted?
The frequency of penetration testing depends on various factors, such as the nature of your business, industry regulations and the level of risk you face. Generally, it is recommended to conduct penetration testing at least once a year or whenever significant changes are made to your systems or infrastructure.
- Can’t we rely on automated vulnerability scanners instead?
While automated vulnerability scanners have their place in a security strategy, they cannot replicate the ingenuity and creativity of human attackers. Penetration testing involves skilled ethical hackers who employ manual techniques to uncover complex vulnerabilities that automated scanners might miss. It provides a more comprehensive assessment of your security systems.
- Will penetration testing disrupt our business operations?
Penetration testing is carefully planned and executed to minimise disruptions to your business operations. Ethical hackers work closely with your organisation to ensure that testing is conducted at convenient times and in a controlled manner. They prioritise the security of your systems while minimising any potential impact on day-to-day activities.
- How long does a penetration test typically take?
The duration of a penetration test varies depending on the size and complexity of your systems. It can range from a few days to several weeks. The ethical hacking team will provide you with a clear timeline and keep you informed throughout the process.
- What happens after the penetration test is completed?
After the penetration test is completed, you will receive a detailed report outlining the vulnerabilities identified, their potential impact and recommended remediation actions. This report serves as a valuable roadmap for improving your security posture. The ethical hacking team can also provide guidance and support in implementing the necessary measures to address the identified vulnerabilities.



