Why a Quarterly Business Review is important

In our rapidly evolving business landscape, staying ahead of the competition requires constant adaptation and optimisation. As a business owner, you need to regularly assess your operations, identify areas for improvement and develop strategies to drive growth. This is where a QBR (Quarterly Business Review) from an MSP (Managed Service Provider) comes into play
What is a QBR?
A QBR is a comprehensive review conducted by an MSP, usually every quarter, to evaluate the performance, progress and alignment of your business objectives with the implemented IT strategies. It goes beyond simply analysing data and metrics; it is an opportunity to discuss challenges, uncover opportunities and strengthen the relationship between you and your MSP. Smaller businesses may only receive a QBR once or twice a year but ask your MSP what their processes are around this.
A QBR is not just a mundane business review; it holds significant emotional weight. It evokes feelings of security, reassurance and confidence in the path your business is taking. Knowing that experts are analysing your performance, identifying areas of improvement and providing guidance instils a sense of trust and peace of mind.
The QBR experience is an opportunity to have open, honest conversations about challenges, fears and aspirations. It allows you to express your concerns and receive personalised recommendations tailored to your specific circumstances. The empathetic approach of the MSP, coupled with active listening and understanding, creates an emotional connection that transcends the usual business-client relationship.
Components of a QBR
- Infrastructure Assessment: The MSP assesses the client’s network, hardware, software and other technology infrastructure components. This evaluation helps identify any potential vulnerabilities, outdated systems or areas that require optimisation.
- Performance Analysis: The MSP reviews the client’s technology performance metrics, such as network uptime, response times and system utilisation. This analysis helps identify bottlenecks, areas of improvement or potential risks.
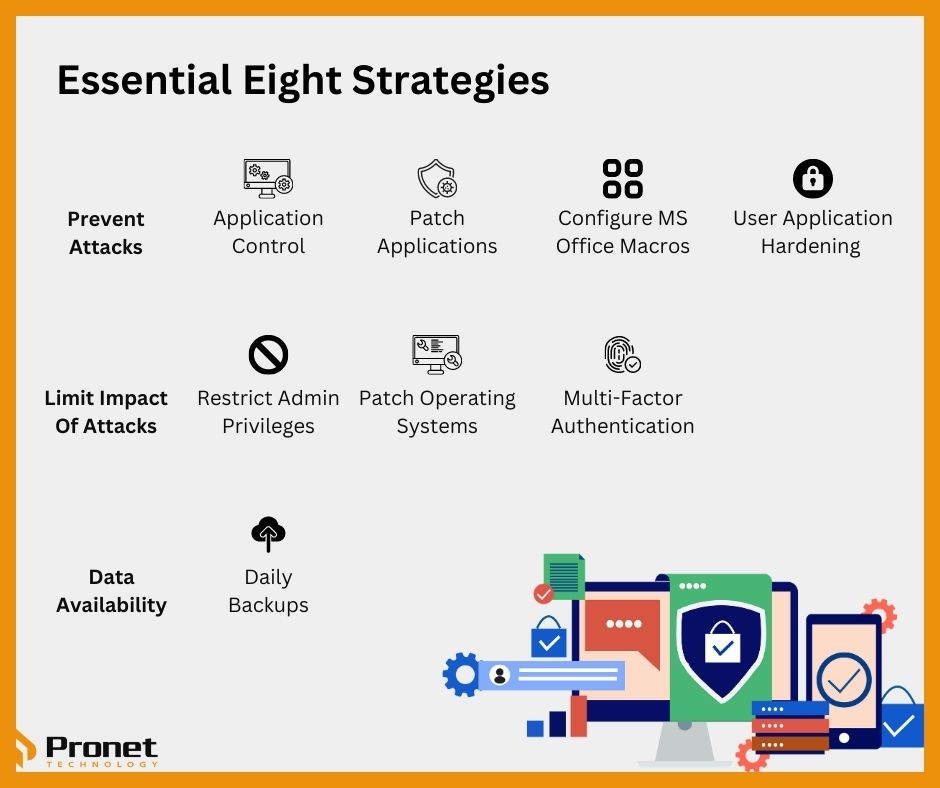
- Security Evaluation: The MSP examines the client’s security posture, including Cyber Security measures, data protection practices and compliance adherence. This assessment helps identify any vulnerabilities or areas where security can be enhanced.
- Service Level Agreement (SLA) Review: The MSP reviews the SLA with the client, ensuring that the agreed-upon service levels are being met. This includes evaluating response times, issue resolution and overall customer satisfaction.
- Future Planning and Recommendations: Based on the assessment findings, the MSP provides recommendations and strategic guidance to the client. This may include suggestions for technology upgrades, process improvements, security enhancements or cost optimisation measures.

The Importance of a QBR from an MSP
A QBR from an MSP holds significant importance for businesses of all sizes. Let’s delve into some key reasons why a QBR is crucial:
Gaining a Holistic View of Your Business
A quarterly business review provides you with a comprehensive overview of your company’s performance during a specific period. It does this by analysing various aspects, including financial performance, operational efficiency, customer satisfaction and employee productivity. By assessing these critical areas, you can identify strengths, weaknesses and areas for improvement. It allows you to identify what areas of your business are excelling and which ones require attention. By recognising your strengths, you can leverage them to gain a competitive advantage. Additionally, addressing weaknesses helps you minimise risks and enhance overall performance.
Uncovering Growth Opportunities
Through a QBR, an MSP can identify untapped growth opportunities that may have gone unnoticed. Analysing market trends, customer feedback and industry benchmarks can provide valuable insights into new markets, product enhancements and innovative strategies to drive business growth.
Enhancing Collaboration and Alignment
A QBR fosters collaboration and alignment within your organisation. By involving key stakeholders, such as department heads and senior management, in the review process, you can ensure that everyone is on the same page regarding goals, challenges and strategies. This collaborative approach promotes a unified vision and encourages teamwork.
Optimising Operational Efficiency
Identifying inefficiencies in your operations is vital for streamlining processes and maximising productivity. An MSP conducting a QBR can analyse your workflows, technology infrastructure and resource allocation to pinpoint areas where improvements can be made. By optimising operational efficiency, you can reduce costs, enhance customer service and achieve better overall performance.
Strengthening IT Infrastructure
A robust IT infrastructure is essential for business success in today’s digital age. A QBR from an MSP can evaluate your current IT systems, Cyber Security measures and data management practices. They can identify vulnerabilities and recommend solutions to enhance your IT infrastructure’s reliability, security and scalability.
Strategic Planning and Risk Mitigation
A QBR enables you to develop effective strategic plans and mitigate potential risks. By examining market trends, competitive landscape and emerging technologies, an MSP can help you formulate strategies that align with your business goals. Additionally, they can identify risks and provide proactive measures to minimise their impact.
Strengthens the Relationship with your MSP
A QBR serves as a bridge between you and your MSP. It fosters open communication, collaboration, and a deeper understanding of your unique business needs. This strengthened partnership allows the MSP to provide tailored solutions and support, ensuring your business thrives. When your MSP invests time and effort in conducting a QBR, it also demonstrates its commitment to your success. The personalised attention, proactive approach and customised recommendations leave you feeling valued and supported, leading to higher client satisfaction and long-term loyalty.

Learning your Business’ Technology Score
When an MSP completes a QBR for your business, oftentimes, you will receive a technology score. The concept of a technology score can vary depending on the specific MSP or service provider you are working with. It is not a universally standardised metric, but rather a subjective evaluation conducted by the MSP based on various factors related to your business’s technology infrastructure and performance.
The technology score typically reflects the MSP’s assessment of your business’s overall technology health, efficiency and alignment with industry best practices. It may consider factors such as:
- Infrastructure: The MSP evaluates the robustness and scalability of your network, servers, storage and other hardware components. They assess whether your infrastructure meets the requirements of your business operations and future growth.
- Security: The MSP examines your Cyber Security measures, including firewalls, antivirus software, data encryption, access controls and employee training. They look for potential vulnerabilities and weaknesses in your security posture.
- Software and Applications: The MSP reviews the software and applications you use, assessing their relevance, performance and integration capabilities. They may consider factors such as licencing compliance, software updates and utilisation efficiency.
- Performance and Reliability: The MSP evaluates the performance and reliability of your technology systems, including network uptime, response times and system availability. They may analyse historical data and metrics to identify areas for improvement.
- IT Governance and Processes: The MSP assesses your IT governance structure, policies and processes. This includes evaluating IT documentation, change management practices, backup and disaster recovery plans, and adherence to industry standards.
Based on these factors, the MSP assigns a technology score to provide you with an indication of how well your business’s technology environment is performing and where improvements can be made. The score may be presented as a numerical value, a rating scale or a qualitative assessment, depending on the MSP’s methodology.
A QBR from an MSP is a critical component for achieving business success. It provides a holistic view of your organisation, uncovers growth opportunities, enhances collaboration, optimises operational efficiency, strengthens IT infrastructure and facilitates strategic planning and risk mitigation. By regularly conducting QBRs, you can stay ahead of the competition, adapt to market changes and drive growth. Remember to involve key stakeholders, seek a reliable MSP and embrace the insights and recommendations provided through the QBR process.
It’s important to note that each MSP may have its own methodology for calculating the technology score, so the specific details may vary. It’s best to consult with your MSP directly to understand how they determine and interpret the technology score for your business.

FAQs about QBRs
- What is the purpose of a QBR?
A QBR aims to evaluate your business performance, identify improvement areas and develop growth strategies. It provides a comprehensive analysis of your operations and fosters collaboration within your organisation.
- How often should QBRs be conducted?
Quarterly QBRs are typically recommended, as they provide a balanced frequency for evaluation and allow for timely adjustments. However, the frequency can be adjusted based on your business needs and industry dynamics.
- Who should be involved in the QBR process?
A QBR should involve key stakeholders from different departments within your organisation. This includes senior management, department heads and individuals responsible for key areas such as finance, operations, marketing, HR and IT. By involving a diverse range of perspectives, you can ensure comprehensive insights and foster collaboration.
- How long does a QBR typically take?
The duration of a QBR can vary depending on the size and complexity of your business. Generally, it can range from a few hours to a full day. It is important to allocate sufficient time to thoroughly discuss each aspect of the review and develop actionable plans.
- What outcomes can I expect from a QBR?
A QBR can deliver several valuable outcomes for your business. These include a clear understanding of your business performance, identified growth opportunities, actionable recommendations for improvement, enhanced collaboration and aligned strategic plans. It also provides an opportunity to address any concerns or challenges faced by your organisation.